Use Vm And Vlan To Prevent Ransomware - Use application control on critical systems. Secure your infrastructure against vm ransomware. In this article, we discussed the potential impact of ransomware attacks on vmware systems, best practices for preventing. A proper defense requires both new tools and techniques. The answer to ransomware is not as simple as a backup solution, though. More hackers are using vms as an access point to install and deploy encrypted.
More hackers are using vms as an access point to install and deploy encrypted. Use application control on critical systems. The answer to ransomware is not as simple as a backup solution, though. Secure your infrastructure against vm ransomware. A proper defense requires both new tools and techniques. In this article, we discussed the potential impact of ransomware attacks on vmware systems, best practices for preventing.
A proper defense requires both new tools and techniques. More hackers are using vms as an access point to install and deploy encrypted. In this article, we discussed the potential impact of ransomware attacks on vmware systems, best practices for preventing. The answer to ransomware is not as simple as a backup solution, though. Use application control on critical systems. Secure your infrastructure against vm ransomware.
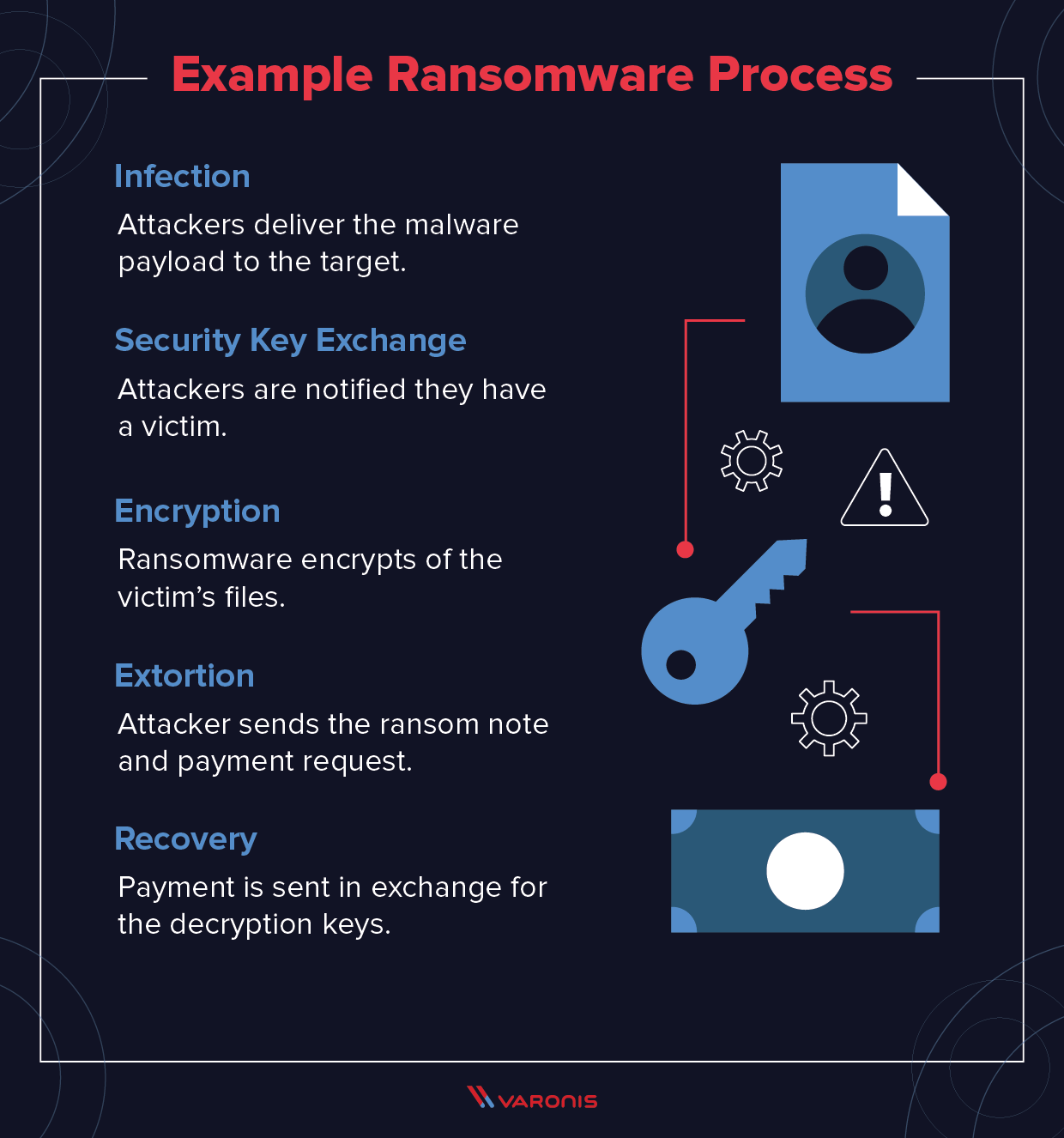
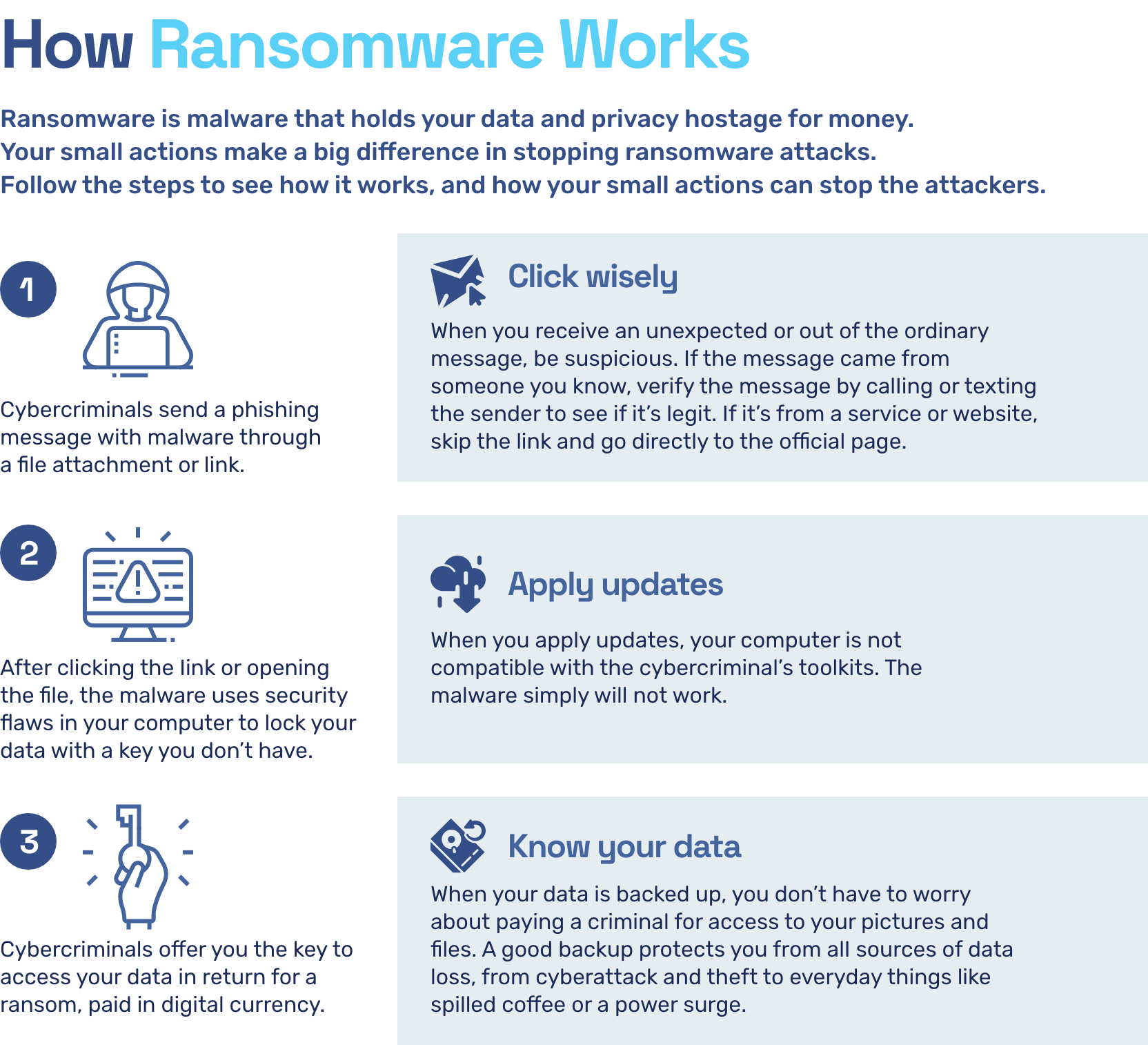
How to Prevent Ransomware? A Quick Guide to Protect Your Company Data
A proper defense requires both new tools and techniques. Secure your infrastructure against vm ransomware. Use application control on critical systems. In this article, we discussed the potential impact of ransomware attacks on vmware systems, best practices for preventing. More hackers are using vms as an access point to install and deploy encrypted.
How To Prevent Ransomware The Definitive Guide
More hackers are using vms as an access point to install and deploy encrypted. Secure your infrastructure against vm ransomware. The answer to ransomware is not as simple as a backup solution, though. A proper defense requires both new tools and techniques. Use application control on critical systems.
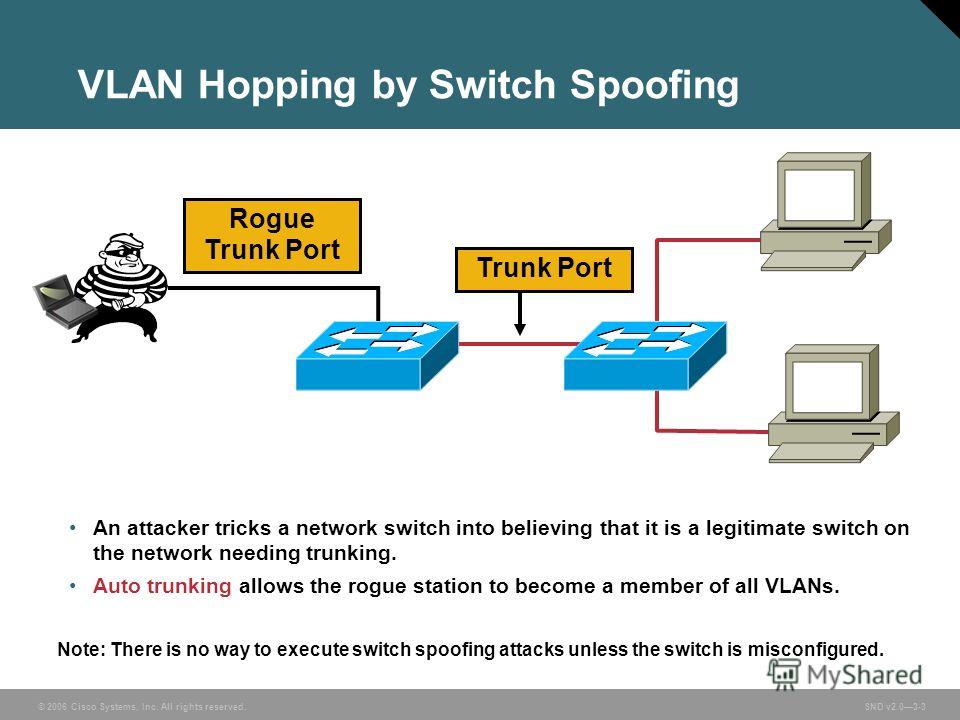
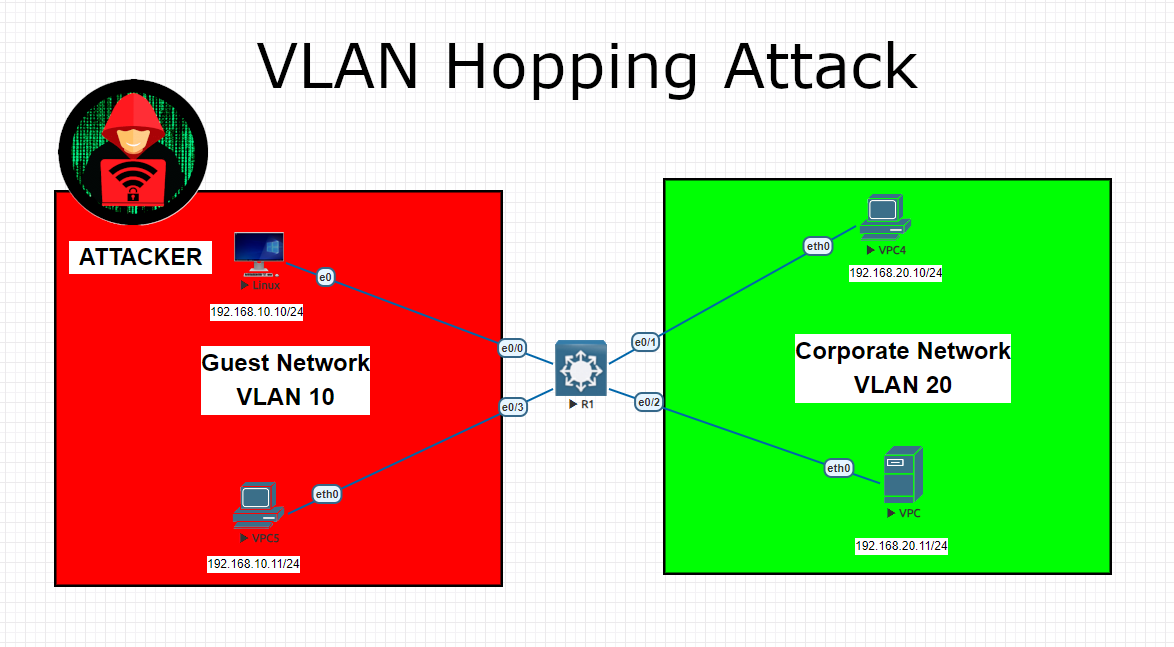
VLAN Hopping Attack NetMe
A proper defense requires both new tools and techniques. The answer to ransomware is not as simple as a backup solution, though. Secure your infrastructure against vm ransomware. In this article, we discussed the potential impact of ransomware attacks on vmware systems, best practices for preventing. Use application control on critical systems.
What is VTP (VLAN Trunking Protocol) ? Baris Kaan Yuksel
A proper defense requires both new tools and techniques. Secure your infrastructure against vm ransomware. More hackers are using vms as an access point to install and deploy encrypted. In this article, we discussed the potential impact of ransomware attacks on vmware systems, best practices for preventing. Use application control on critical systems.
Ransomware Detection and Prevention Omega Systems
More hackers are using vms as an access point to install and deploy encrypted. In this article, we discussed the potential impact of ransomware attacks on vmware systems, best practices for preventing. Secure your infrastructure against vm ransomware. A proper defense requires both new tools and techniques. Use application control on critical systems.
How to Prevent Ransomware Attacks On Industrial Networks Cyber
Secure your infrastructure against vm ransomware. More hackers are using vms as an access point to install and deploy encrypted. In this article, we discussed the potential impact of ransomware attacks on vmware systems, best practices for preventing. A proper defense requires both new tools and techniques. The answer to ransomware is not as simple as a backup solution, though.
How to Prevent Ransomware Essential Tips, Tactics and Techniques
A proper defense requires both new tools and techniques. Use application control on critical systems. The answer to ransomware is not as simple as a backup solution, though. Secure your infrastructure against vm ransomware. More hackers are using vms as an access point to install and deploy encrypted.
You Can Download Our Free Infographic On Ransomware Here
The answer to ransomware is not as simple as a backup solution, though. A proper defense requires both new tools and techniques. In this article, we discussed the potential impact of ransomware attacks on vmware systems, best practices for preventing. Use application control on critical systems. More hackers are using vms as an access point to install and deploy encrypted.
How To Prevent Ransomware The Basics
A proper defense requires both new tools and techniques. The answer to ransomware is not as simple as a backup solution, though. Secure your infrastructure against vm ransomware. More hackers are using vms as an access point to install and deploy encrypted. Use application control on critical systems.
7 Point How To Prevent Ransomware Attack?
More hackers are using vms as an access point to install and deploy encrypted. Use application control on critical systems. Secure your infrastructure against vm ransomware. The answer to ransomware is not as simple as a backup solution, though. A proper defense requires both new tools and techniques.
In This Article, We Discussed The Potential Impact Of Ransomware Attacks On Vmware Systems, Best Practices For Preventing.
The answer to ransomware is not as simple as a backup solution, though. More hackers are using vms as an access point to install and deploy encrypted. Use application control on critical systems. A proper defense requires both new tools and techniques.


.jpg?width=1280&height=720&name=What is Ransomware (1).jpg)