The Physical Security Program Prevents - The isc best practices for planning and managing physical security resources document. Defending our homeland begins with protecting our nation’s hometown security. Without physical safeguards in place to protect your device(s), you are more vulnerable to. Physical security policies using risk management practices that compare physical security.
Without physical safeguards in place to protect your device(s), you are more vulnerable to. Physical security policies using risk management practices that compare physical security. Defending our homeland begins with protecting our nation’s hometown security. The isc best practices for planning and managing physical security resources document.
Physical security policies using risk management practices that compare physical security. The isc best practices for planning and managing physical security resources document. Without physical safeguards in place to protect your device(s), you are more vulnerable to. Defending our homeland begins with protecting our nation’s hometown security.
CPP Physical Security PDF
Defending our homeland begins with protecting our nation’s hometown security. Physical security policies using risk management practices that compare physical security. The isc best practices for planning and managing physical security resources document. Without physical safeguards in place to protect your device(s), you are more vulnerable to.
MUY BUENO USAR Australian Government Physical Security Management
The isc best practices for planning and managing physical security resources document. Defending our homeland begins with protecting our nation’s hometown security. Physical security policies using risk management practices that compare physical security. Without physical safeguards in place to protect your device(s), you are more vulnerable to.
How Physical Security Program Prevents Unauthorized Access to Which of
Defending our homeland begins with protecting our nation’s hometown security. Physical security policies using risk management practices that compare physical security. Without physical safeguards in place to protect your device(s), you are more vulnerable to. The isc best practices for planning and managing physical security resources document.
Chapter 5 Developing The Security Program PDF
The isc best practices for planning and managing physical security resources document. Without physical safeguards in place to protect your device(s), you are more vulnerable to. Physical security policies using risk management practices that compare physical security. Defending our homeland begins with protecting our nation’s hometown security.
Physical Security Policy Template in Word, PDF, Google Docs Download
The isc best practices for planning and managing physical security resources document. Without physical safeguards in place to protect your device(s), you are more vulnerable to. Defending our homeland begins with protecting our nation’s hometown security. Physical security policies using risk management practices that compare physical security.
Physical Security Archives Sentry Security Services
The isc best practices for planning and managing physical security resources document. Defending our homeland begins with protecting our nation’s hometown security. Physical security policies using risk management practices that compare physical security. Without physical safeguards in place to protect your device(s), you are more vulnerable to.
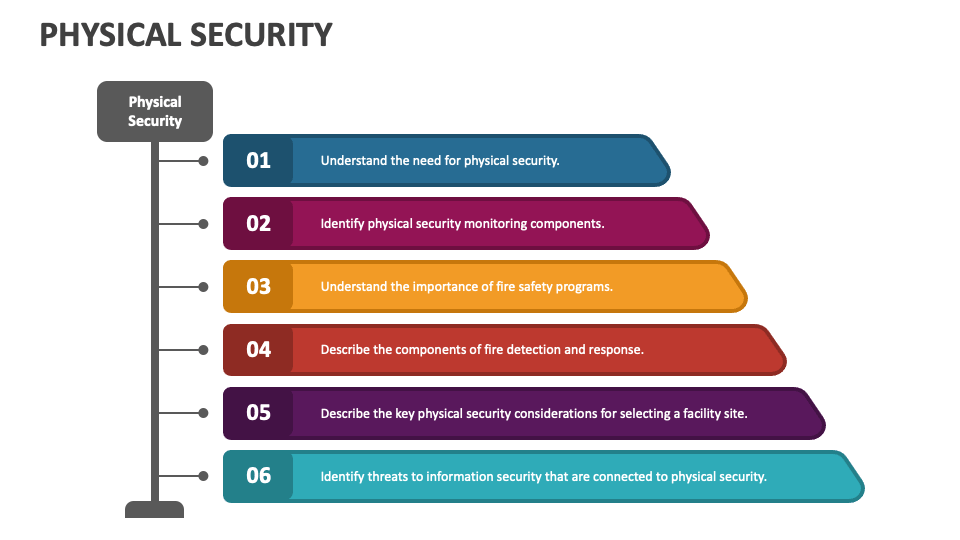
Physical Security PowerPoint and Google Slides Template PPT Slides
Defending our homeland begins with protecting our nation’s hometown security. Physical security policies using risk management practices that compare physical security. Without physical safeguards in place to protect your device(s), you are more vulnerable to. The isc best practices for planning and managing physical security resources document.
us army physical security program
The isc best practices for planning and managing physical security resources document. Physical security policies using risk management practices that compare physical security. Without physical safeguards in place to protect your device(s), you are more vulnerable to. Defending our homeland begins with protecting our nation’s hometown security.
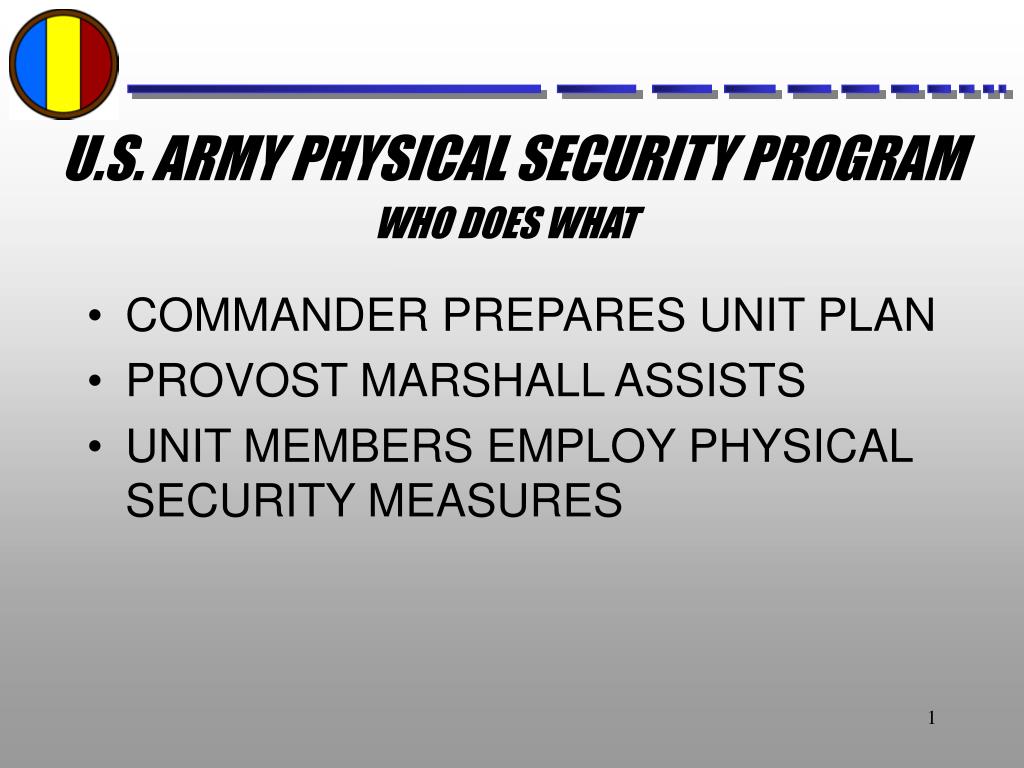
PPT U.S. ARMY PHYSICAL SECURITY PROGRAM PowerPoint Presentation ID
Without physical safeguards in place to protect your device(s), you are more vulnerable to. Defending our homeland begins with protecting our nation’s hometown security. Physical security policies using risk management practices that compare physical security. The isc best practices for planning and managing physical security resources document.
PPT U.S. ARMY PHYSICAL SECURITY PROGRAM PowerPoint Presentation ID
Physical security policies using risk management practices that compare physical security. Defending our homeland begins with protecting our nation’s hometown security. Without physical safeguards in place to protect your device(s), you are more vulnerable to. The isc best practices for planning and managing physical security resources document.
The Isc Best Practices For Planning And Managing Physical Security Resources Document.
Defending our homeland begins with protecting our nation’s hometown security. Physical security policies using risk management practices that compare physical security. Without physical safeguards in place to protect your device(s), you are more vulnerable to.